The XYLEM - XYZ Protocol: Engineering Immutable Truth in the Age of Synthetic Media
As digital decay and synthetic misinformation undermine web integrity, the XYZ Protocol engineers a sovereign pipeline to restore data ground-truth. By merging automated web-harvesting with decentralized Proof of Existence (PoE), this architecture transforms ephemeral web content into permanent, verifiable digital assets. Harmonic System,Bridging Web Ingestion and Bitcoin Immutability: A Decentralized Framework for Data Integrity
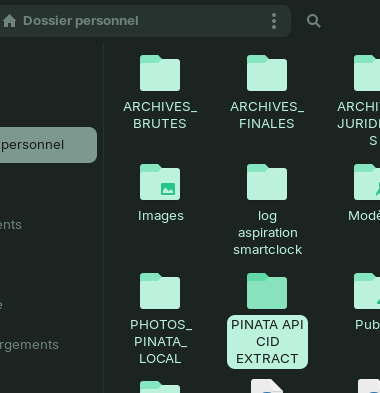
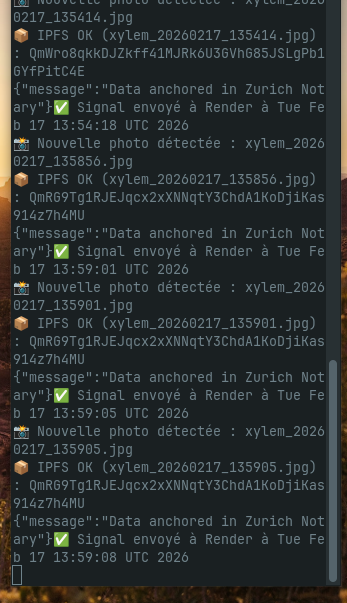
OTo circumvent the volatility of live web environments, the XYZ Protocol implements a proprietary localized ingestion layer designed for high-fidelity asset recovery. By capturing snapshots in a local buffer, the system decouples the intensive data mining phase from the cryptographic settlement process..
BUHS on Paragraph.xyz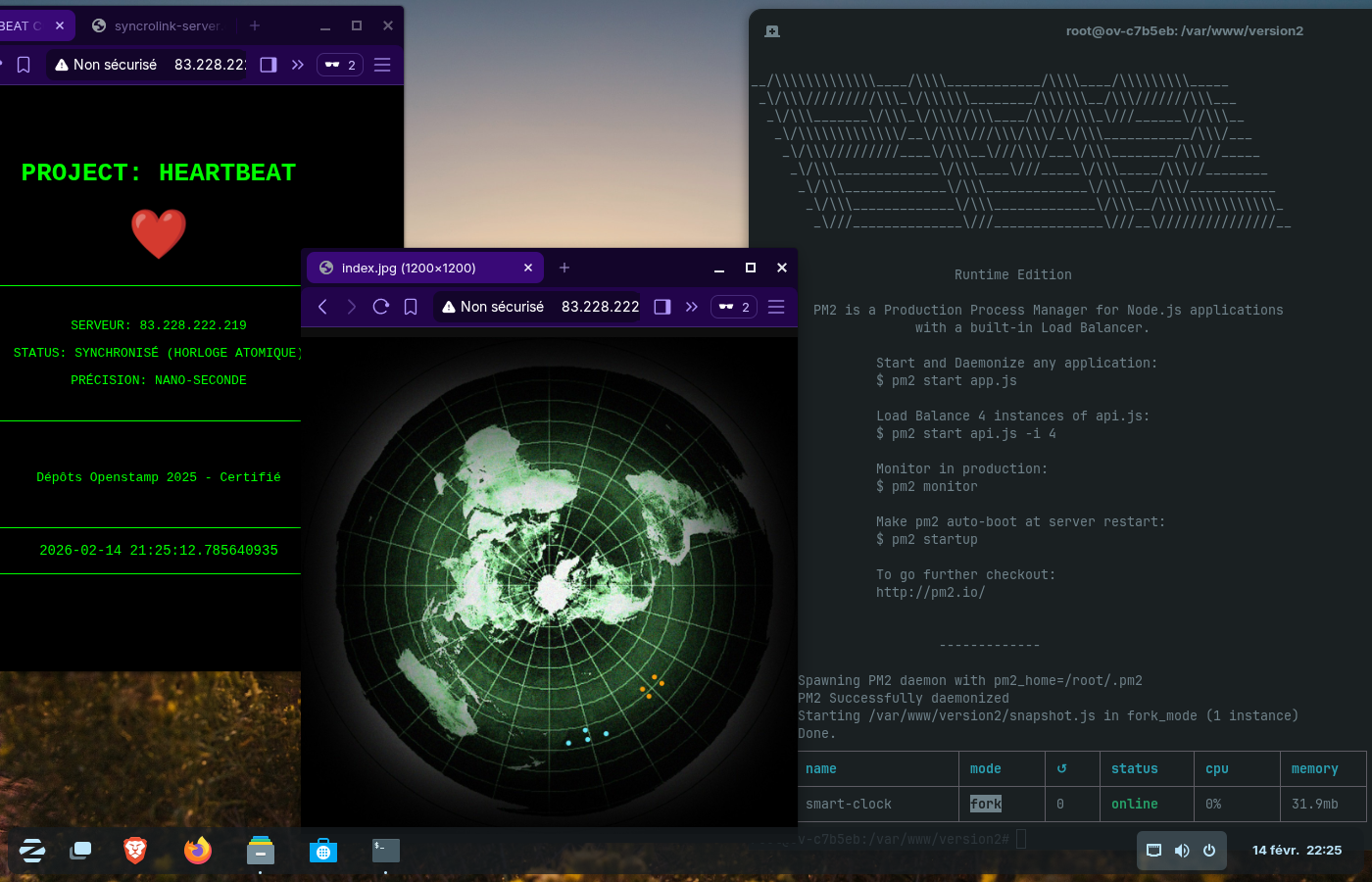
System Capabilities
This is where the protocol moves from simple storage to DeepTech Certification.
We specialize in Recursive OptimizationHashing Algorithm: Each file undergoes a SHA-256 cryptographic hash. This creates a unique digital fingerprint. Even changing a single pixel in a photo or a comma in a text file will result in a completely different fingerprint. Merkle Tree Integration: The OpenTimestamps (OTS) protocol aggregates multiple file hashes into a single Merkle Tree. The root of this tree is then "stamped" onto the Bitcoin blockchain. Trustless Verification: Because the proof is on the Bitcoin ledger, you do not need a third-party notary. The math proves that the file existed in that exact state at that specific time.
INITIALIZE LINK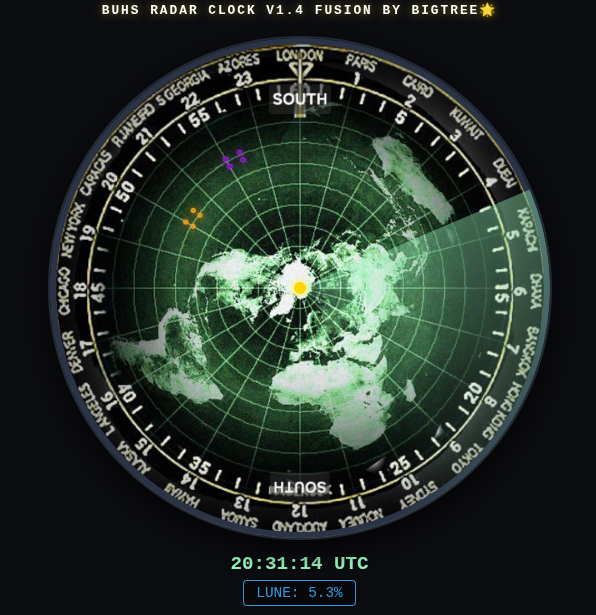
System Artefacts